A blockchain that markets itself as “digital silver” just proved it can rewind time — erasing 32 minutes of transactions because a month-old patch never reached the people who needed it most.
On Friday 25 April, Litecoin’s network executed a rare 13-block chain reorganisation after attackers exploited a vulnerability in the MWEB (MimbleWimble Extension Blocks) privacy layer. The reorg stretched from block 3,095,930 to block 3,095,943 and took over three hours to fully resolve. Initial monitoring tools flagged it as a potential 51% attack. The Litecoin Foundation insists it was a bug. The truth, as always, is messier — and far more damning.
The Anatomy of a Calculated Strike
This was not some opportunistic script kiddie stumbling upon a glitch. Blockchain data reveals the attacker pre-funded a wallet via a Binance withdrawal roughly 38 hours before the exploit went live. The destination address was already configured to swap LTC into ETH on a decentralised exchange. This was a surgical operation.
The attack combined two separate vulnerabilities. First, a consensus bug in MWEB (commit 1dcbf3f) that allowed the kernel sum to become unbalanced, enabling invalid peg-out transactions — essentially unlocking coins from the privacy layer without proper authorisation. Second, a denial-of-service vulnerability that could knock updated mining nodes offline.
Here is where it gets clever. By hitting patched miners with the DoS attack, the attacker forced the network to temporarily rely on nodes running the vulnerable code. Those unpatched nodes happily accepted the invalid MWEB transaction as legitimate. The attacker then routed the coins to decentralised exchanges before anyone could react.
NEAR Intents, a cross-chain bridge, reported approximately $600,000 in exposure from double-spend attacks executed during the fork window. The bridge has pledged to compensate affected users and has suspended LTC services until stability is confirmed.
The 37-Day Disclosure Scandal
The exploit itself is concerning. But the disclosure timeline is where this story turns genuinely uncomfortable for the Litecoin team.
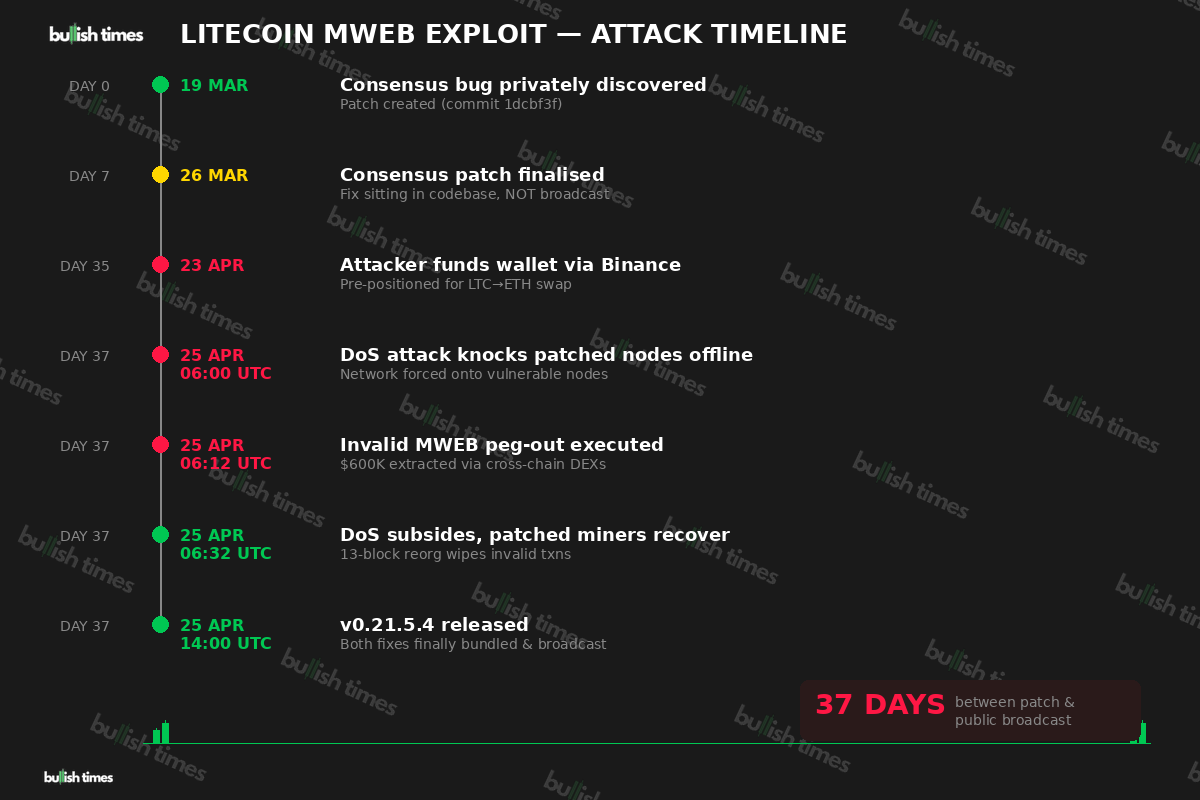
Security researcher bbsz, working with the SEAL911 emergency response group, pulled the patch timeline from Litecoin’s public GitHub commit log. The consensus vulnerability was privately discovered and patched between 19 and 26 March — a full 37 days before the 25 April attack. The separate DoS vulnerability was only patched on the morning of the attack itself.
Both fixes were then hastily bundled into the v0.21.5.4 release that same afternoon.
The critical problem? The consensus fix had been sitting in the codebase for over a month, but it was never publicly broadcast or made a mandatory upgrade for mining pools. This created a two-tier network: some miners ran the patched code, others remained on the vulnerable version. The attackers appear to have known exactly which pools had updated and which had not.
As bbsz bluntly noted, a zero-day — by definition — is a vulnerability that defenders are unaware of at the time of attack. The GitHub history suggests the Litecoin team knew about the consensus bug and fixed it privately weeks in advance. The fix simply never reached the broader network in time.
The Litecoin Foundation has not publicly addressed the GitHub timeline as of Monday morning.
The Immutability Myth Takes Another Hit
For years, proof-of-work advocates have marketed blockchains as immutable ledgers where transactions cannot be reversed. Litecoin just demonstrated that a coordinated attack, combined with unpatched nodes, can force the network to rewrite its own history.
The 13-block reorg wiped out roughly 32 minutes of transaction history. Yes, the invalid transactions were removed. Yes, all “legitimate” transactions during that window were preserved. But the philosophical damage is done: how many confirmations make a transaction feel secure if a single bug can erase 13 blocks?
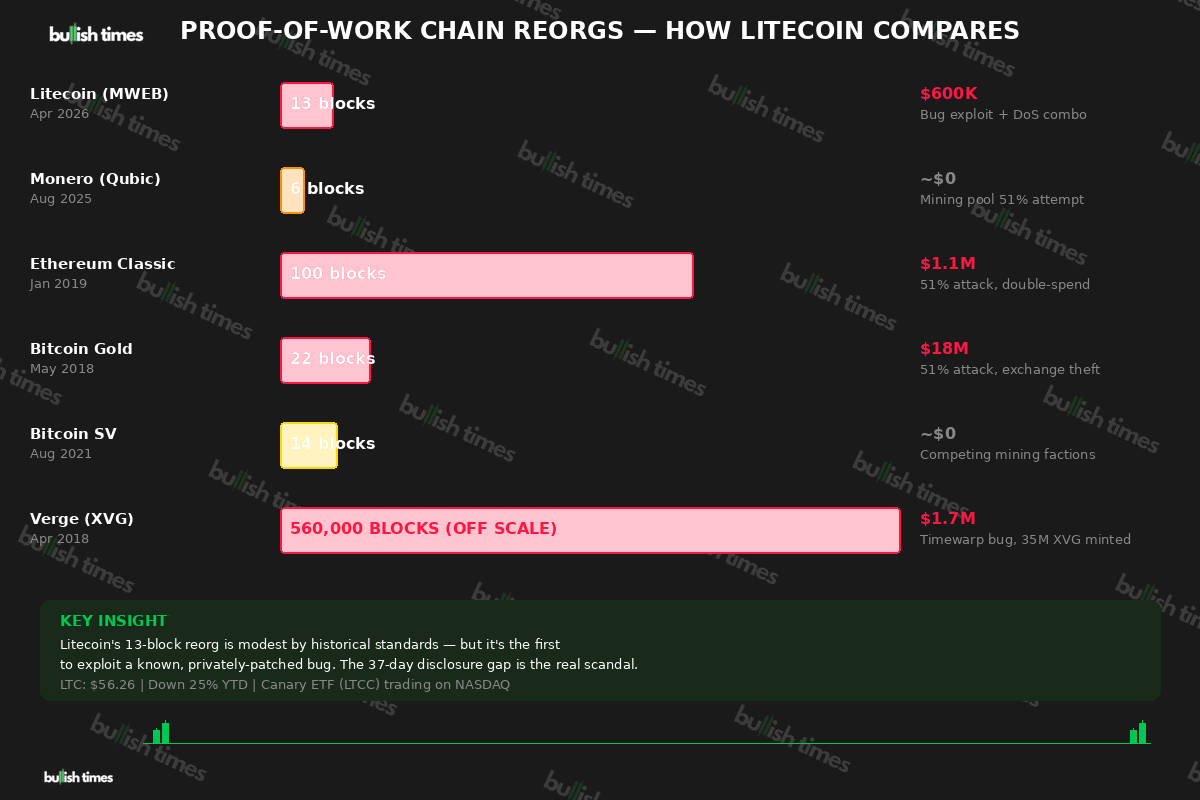
Predictably, rival chains have been quick to twist the knife. An XRP Ledger validator argued that proof-of-work is “the worst security model” because “you’re only as secure as someone else is willing to spend more to attack the network than PoW is incentivising miners.” Solana’s official account openly trolled Litecoin on X. Even within the Litecoin community, the r/litecoin subreddit has been consumed by debate over whether this constitutes a genuine attack or merely a “defensive reorg.”
What This Means for Litecoin — and PoW Security
The immediate fallout is limited. LTC is trading at approximately $56.26, down just 1% on the day. No sharp market reaction. The Canary Litecoin ETF (LTCC) continues trading on NASDAQ. The LitecoinVM zero-knowledge rollup testnet, which recorded nearly 100,000 transactions in its first 24 hours earlier this month, remains unaffected.
But the structural questions linger. MWEB has been live since May 2022, with over 260,000 LTC locked in the extension layer and 90% node support. This was its first known major exploit — and it exposed not a fringe edge case, but a fundamental flaw in the protocol-level accounting logic.
More broadly, the incident highlights a tension at the heart of every proof-of-work network. Unlike chains with smaller, more centralised validator sets that can coordinate emergency patches through private channels within hours, PoW networks rely on independent mining pools choosing when — and whether — to upgrade. That decentralised upgrade model is a feature during normal operations. It becomes a critical vulnerability when a patch needs to reach every participant before an attacker exploits the gap.
April 2026 has now seen over $630 million in DeFi exploit losses, including the $292 million KelpDAO bridge drain and the $280 million Drift Protocol hack. Litecoin’s $600,000 exposure is a rounding error by comparison. But the principle is the same: known vulnerabilities, slow patches, extracted value.
The Litecoin team says the bug is fully patched and the network is stable. They are probably right. But when your blockchain’s best defence is “we rewound time and it worked out,” you have already lost the argument about immutability.
This is a developing story. Bullish Times will update if the Litecoin Foundation addresses the 37-day disclosure timeline.